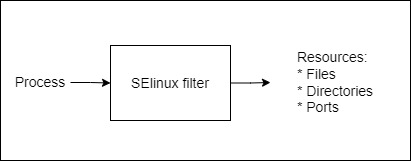
SELinux is a set of security rules using which we can control the processes/application that can access specific files, folders and ports. These processes, files, folders and ports has a special security label called SELinux context. The label called context can be:
- user
- role
- type
- sensitivity.
Installing the below packages can help in troubleshoot SElinux related issues
[root@centos9vm ~]# dnf install policycoreutils-python-utils.noarch
[root@centos9vm ~]# dnf install setroubleshoot.x86_64
The SELinux policy determines if a process or application such as httpd, etc can access a files, folders or port. By default the SELinux policy blocks all access to files, folders and ports.
SELinux application specific policies is defined by the application developers. These policies define what actions are allowed for execution, and what access is allowed. The default policy enabled in RHEL/CentOS called “targeted policy”.
Selinux Context (label) has the below parameters:
- SElinux user
- Role
- Type
- Level
If we take example of a Apache web service, the httpd process usually access the folders “/var/ww/html”, “/var/tmp”, “/tmp”, etc.
The Type context associated with httpd service is httpd_t. The Type context associated with the folder “/var/ww/html” is “httpd_sys_content_t“, the port is “http_port_t“, etc.
The SELinux context can be displayed when using commands such as ps, ls, cp, mkdir. etc by using the “-Z” switch. For example:
[root@shiju-test ~]# ps -axZ | grep http
system_u:system_r:httpd_t:s0 11675 ? Ss 0:00 /usr/sbin/httpd -DFOREGROUND
system_u:system_r:httpd_t:s0 11676 ? S 0:00 /usr/sbin/httpd -DFOREGROUND
[root@shiju-test ~]# ls -Z /var/www
drwxr-xr-x. root root system_u:object_r:httpd_sys_script_exec_t:s0 cgi-bin
drwxr-xr-x. root root system_u:object_r:httpd_sys_content_t:s0 html
Copying and Moving files
When moving a file or folder, the SELinux context is preserved by default.
[root@shiju-test ~]# mv /tmp/shiju.txt /var/www/html
When copying a file or folder, the SELinux is NOT preserved by default. The switch “-p” is required to carry the SELinux context.
[root@shiju-test ~]# cp /tmp/shiju.txt /var/www/html
[root@shiju-test ~]# ls -Z /var/www/html
[root@shiju-test ~]# cp =p /tmp/shiju.txt /var/www/html
SELinux configuration file
Configuration file for SELinux is “/etc/selinux/config”
SELinux can be configured in three modes:
- Enforced : Policies are enforced and logging is enabled
- Permissive : Policies are actually disabled but logging is enabled as the policies are enabled
- Disabled : Policies are disabled and logging is also not enabled.
Command to verify the mode in which SELinux is running:
[root@shiju-test ~]# getenforce
Command to switch to disabled mode:
[root@shiju-test ~]# setenforce 0
Command to switch to permissive mode:
[root@shiju-test ~]# setenforce 1
In RHEL, the SElinux can be fully disabled during the boot process itself if needed. To do that, enter the grub prompt during the bootup, and in the Kernel parameter add one of the below value:
- selinux=0
- enforcing=0
- enforcing=1
Save changes and procced with the booting process.
SELinux Logs
SELinux logs useful information such as info about access denied, etc. The default log file is:
/var/log/audit/audit.log
An example to understand SELinux context
- Use a system in which SELinux is enabled. The command “getenforce” will show the present SELinux setting.
- Install httpd server and ensure firewalld is disabled in the host .
- Create an html file name index.html displaying a line “Hello World – var – html“
- Allow everyone to access the page by issuing the command:
- chmod 755 /var/www/html/index.html
- Verify if everyone can see the web page by accessing the server via a web browser. It should work while selinux is also enabled.
- Create a new folder named “/virtual”
- Create an html file name /virtual/index.html displaying a line “Hello World – virtual – html“.
- Add the following lines in your apache webserver’s configuration file httpd.conf:
<Directory “/virtual”>
AllowOverride None
# Allow open access:
Require all granted
</Directory>
- In the httpd.conf file, edit the line that starts with “DocumentRoot” so that it looks like:
DocumentRoot “/virtual” - Restart apache by running the command “systemctl restart httpd”
- The service may fail
You may not be able to see the web page is accessed via browser since SELinux may be blocking access to “/virtual/index.html”
Check the log file “/var/log/audit/audit.log” for any entry related to it like:
- type=AVC msg=audit(1523351308.296:598): avc: denied { getattr } for pid=1247 comm=”httpd” path=”/virtual/index.html” dev=”xvda2″ ino=25270803 scontext=system_u:system_r:httpd_t:s0 tcontext=unconfined_u:object_r:default_t:s0 tclass=file
If you disable SELinux temporarily by issuing the command “setenforce 0” or permanently by editing the file “/etc/selinux/config” you will see that the file gets displayed.
How to get the new page displayed with SELinux?
We can change the context of a file by using either:
- Temporary method
- chcon
- Permanent method
- fcontext
- restorecon
To make the webpage “/virtual/index.html” accessible by http server while SELinux is enforced, run the following command:
[root@shiju-test ~]# chcon -R -t httpd_sys_content_t /virtual/
Check the result by running the following command:
[root@shiju-test ~]# ls -Z /virtual
-rwxr-xr-x. 1 root root system_u:object_r:httpd_sys_content_t:s0 43 Feb 12 19:59 index.html
Now the new webpage should get displayed via the browser
The set of files that holds the default context of files and folder are located in “/etc/selinux/targeted/contexts/files/”
As the chcon command is a temporary way to change context permission, restarting the node or issuing the restorecon command will revert context attached to a file to the value mentioned in the above files.
To restore the context to default settings as mentioned in SELinux policy use the following command:
root@shiju-test ~]# restorecon -Rv /virtual/
Relabeled /virtual from system_u:object_r:httpd_sys_content_t:s0 to system_u:object_r:default_t:s0
Relabeled /virtual/index.html from system_u:object_r:httpd_sys_content_t:s0 to system_u:object_r:default_t:s0
Command to view the default SELinux policy settings is as below. You may use “grep” function to display selective results
root@shiju-test ~]# ls -lZ /virtual/
-rwxr-xr-x. 1 root root system_u:object_r:default_t:s0 43 Feb 12 19:59 index.html
Semanage commands
The below command lists all context policies that will be read by default
[root@shiju-test ~]# semanage fcontext -l
We can add an SELinux Policy by using semanage fcontext commands so that the same can be used when “restorecon” command is used.
Mentioned below command changes the context of all files in “/virtual” folder
[root@shiju-test ~]# semanage fcontext -a -t httpd_sys_content_t ‘/virtual(/.*)?’
root@shiju-test ~]# restorecon -Rv /virtual/
Listening ports associated with a service
Troubleshooting SELinux is easy by using the “setroubleshoot-server” that can be installed using the command “yum install setroubleshoot-server”